First run:
Copy headers (with cookies) of POST license request from browser to headers.py like dictionary.
pip install -r requirements.txt # if doesn't work try pip3
py l3.py
Input MPD URL: https://site.ru/.../.../filename.mpd
License URL: https://cms.35mm.online/umbraco/api/products/473/drm/widevine?platform=BROWSER&type=MOVIE
Works only if the site does not require specific json-formatted data in the license request. And if it requires and you want to add its support, write to issues specifying the required json-formatted fields and the algorithm for their formation (if not static).
Examples:
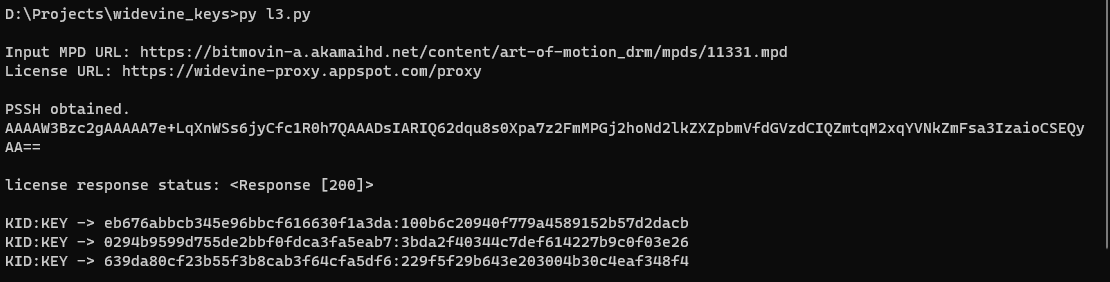
- Normal work:
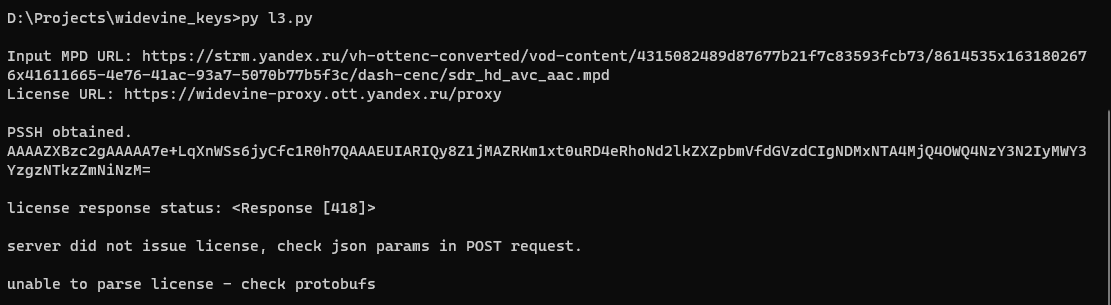
- Server did not issue a license, as it requires additional json-formatted data:
- If "Unable to find PSSH in mpd" - write about this error to issues attaching a link to mpd.
Further about kinopoisk (hello to compatriots):
Not working yet. It is necessary to find out how the POST request is signed (the signature field in the request payload). It looks like a simple hash of sha1, but from the looks of it, this is not it, but the Amazon's AWS Signature Version 4. Or I am doing something wrong and everything is much easier... Any ideas are appreciated, write to issues.